What you should know:
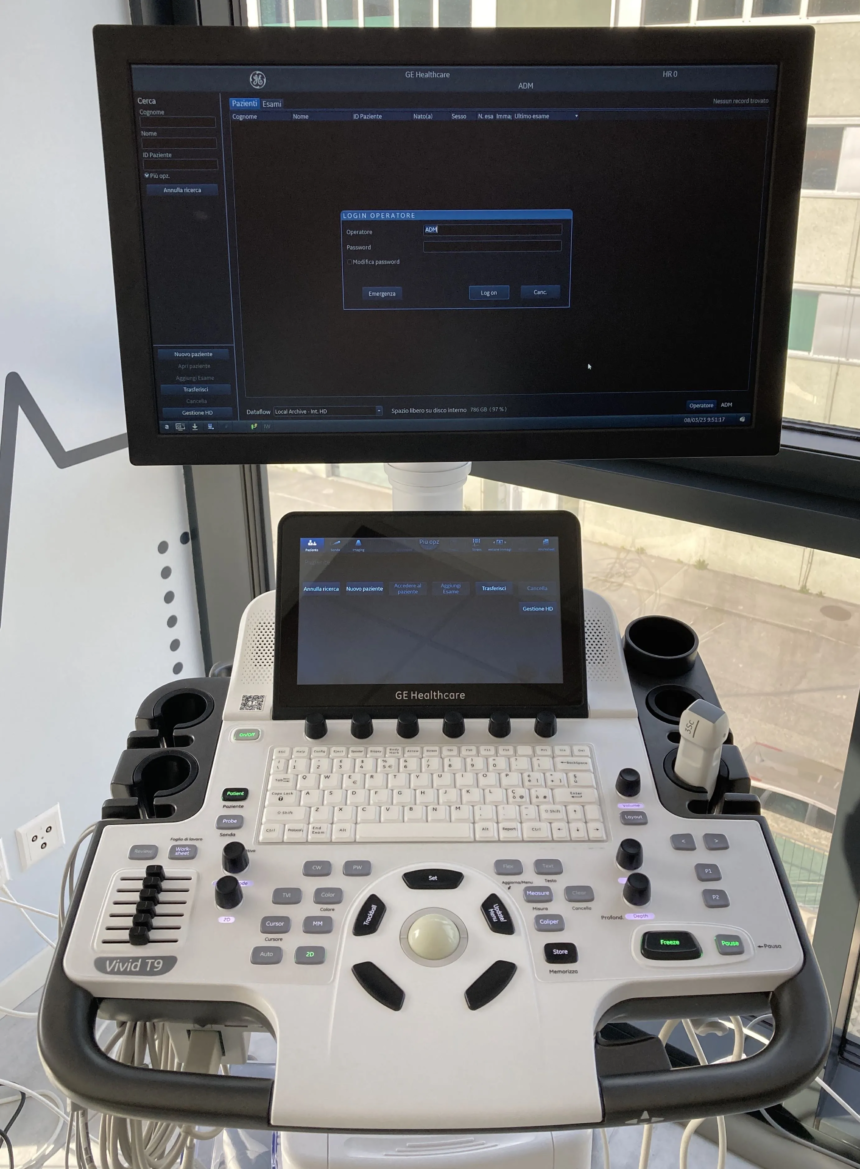
– Security researchers at Nozomi Network Labs to have identified a total of 11 vulnerabilities affecting GE HealthCare's Vivid family of ultrasound devices, its accompanying Common Service Desktop web application, and EchoPAC PC software.
– These vulnerabilities could be exploited by attackers to disrupt critical medical procedures, compromise patient data privacy, and prevent accurate diagnoses.
Vulnerable devices and potential impacts
- Vivid T9 Ultrasound System: An attacker with physical access to the device could potentially deploy ransomware, blocking healthcare providers' access to the system and delaying critical procedures.
- Common Services Desk Web Application: Abuse of vulnerabilities in this application could allow attackers to gain access to the entire ultrasound system.
- EchoPAC PC software: Attackers on the same network as a vulnerable EchoPAC installation could potentially steal or manipulate patient data stored on the software.
Technical details and attack scenarios
The researchers detail different attack scenarios exploiting these vulnerabilities. A concerning scenario involves a two-phase attack against the Vivid T9 system:
- Get local access: Abuse of a vulnerability in the Common Service Desktop application allows an attacker to bypass security restrictions and gain local access to the ultrasound system.
- Code execution and ransomware deployment: Another Common Service Desktop vulnerability allows attackers to execute code with full administrative privileges. This could be used to deploy ransomware, disrupting critical medical procedures.
Ransomware is just one potential consequence. Stolen patient data could be misused or sold on the dark web, posing a significant risk to individuals' privacy.
Risk management and recommendations
GE HealthCare has confirmed that its medical staff has conducted a security risk assessment and concluded that the associated security risk is contained. However, researchers highlight the increasing frequency and complexity of ransomware attacks against healthcare providers.
Recommendations for healthcare providers include:
- Patch systems: Refer to the GE HealthCare Product Security Portal for official fixes and mitigations.
- Physical security: Never leave ultrasound devices unattended, even for a short time.
- Network segmentation: Implement appropriate network segmentation to limit communication between devices and the broader network.
- Firewall rules: For workstations with EchoPAC installed, implement firewall rules to block unnecessary network traffic.