In the early days of industrial use of computers, their requirements were minimal. However, today, data generation has increased exponentially with the widespread use of IoT devices across many industries. Such an abundance of data requires massive computing power, which can only be achieved by deploying large central systems or multiple distributed systems. However, these systems have significant cybersecurity implications. Before discussing the cybersecurity implications associated with various IT systems, it is essential to understand the fundamental difference between operational technology (OT) and information technology (IT) in the IoT domain.
Operational Technology vs. Information Technology (OT vs. IT)
The distinction between operational technology (OT) and information technology (IT) is clear and crucial to the successful operation of a manufacturing plant. OT concerns the operational aspect of a facility, which includes the hardware and software used to control and monitor processes. It includes devices such as SCADA, PLCs, sensors, and other equipment that execute pre-programmed actions to achieve desired results in plant operations.
In contrast, IT manages data and information flows and provides supporting technology for industrial operations. This involves a range of hardware and software, from messaging services to manufacturing execution systems (MES). Although not always essential to the operation of factories, computer systems can significantly improve factory operations by improving efficiency.
Centralized or decentralized computing
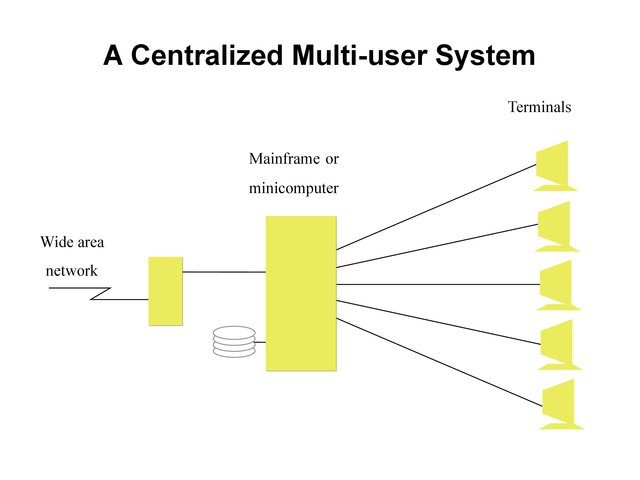
Global network systems are traditionally centralized, with a single server acting as the central node for storing, processing, and routing information across the entire network. This model allowed authorized users and devices to access data from the central server. However, this outdated model has now been replaced by decentralized IT systems.
In decentralized computing systems, there is no central server; instead, there are interconnected clusters with a node at their center. These nodes are connected and the computing power is distributed across multiple nodes, making it a more efficient operating model. Additionally, the possibility of a failure causing the entire system to shut down is minimal.
Distributed computing is an extension of decentralized computing, in which all devices have computing capabilities and are connected via a mesh network. This architecture provides a more resilient IT system but comes at a higher cost.
| Functionality | Centralized IT | Decentralized computing |
| Control | A single entity controls all resources and data | No entity controls all resources and data |
| Data storage | Data is stored in a central location | Data is spread across multiple locations |
| Security | Security is the responsibility of the central authority | Security is distributed among participants |
| Scalability | Scales well to large amounts of data and users | Best scales for small to medium amounts of data and users |
| Cost | Higher cost due to centralized infrastructure and maintenance | Lower cost due to lack of centralized infrastructure |
| Fault Tolerance | A single point of failure can bring down the entire system | Redundancy and distribution reduce the risk of single points of failure |
| Confidentiality | A single entity controls user data | User data is encrypted and distributed, reducing exposure |
| Accessibility | Users must access the central server to use the network | The network can be accessed from anywhere with an Internet connection |
| Resistance to censorship | It is easier for governments or other entities to censor or shut down | Harder for governments or other entities to censor or shut down |
| Consensus algorithm | Not necessary for centralized systems | Required for decentralized systems to ensure consistency and security |
| Smart contracts | This is not possible without a decentralized architecture | Possible with a decentralized architecture |
The challenges of IT cybersecurity
Industrial systems are facing an alarming increase in cybersecurity threats, as evidenced by recent attacks on critical national infrastructure. Hackers have demonstrated the ability to hold entire pipelines for ransom. It is imperative to consider cyberattack protection for every IT system used with automation and IoT.
In a centralized IT model, the central server is the main vulnerability. If compromised, the entire system goes offline and operations can stop. A single point of attack can bring down the entire system. It is therefore crucial to prioritize the protection of the central server.
On the other hand, in a decentralized and distributed model, the attack vector is much broader. Even if one of the nodes or devices is compromised, the rest of the system can remain operational. However, if a security breach goes undetected, malware can spread across the network and infect all nodes and devices.
IoT has also transformed the cybersecurity landscape of industrial systems. The centralized model of IoT architecture uses central servers and the distributed model relies on edge computing. All devices are connected to the Internet and have some data processing capabilities, increasing potential attack vectors for hackers. Therefore, it is essential to follow cybersecurity best practices to protect critical infrastructure in every architecture.
Cybersecurity Best Practices
Industrial systems are increasingly exposed to attacks from sovereign adversaries and malicious hackers. Implementing strong defense systems is the only way to effectively protect against such attacks. Fortunately, the National Institute of Standards and Technology (NIST) and the International Society of Automation (ISA) have established comprehensive guidelines and standards for cybersecurity in the industrial sector. To build a truly resilient ICS, companies must follow these best practices.
Improving industrial cybersecurity: focus on firewalls, encryption and redundancy
Industrial networks continually face threats from cyberattacks, making robust security measures imperative. Firewalls, composed of hardware and software components, are the main line of defense, monitoring and regulating the flow of data based on predefined rules. Proven firewall implementations from trusted vendors are essential for any industrial control system (ICS) deployment.
Encryption is essential to ensure data integrity, particularly against data exfiltration attempts. By encrypting all network communications, sensitive information remains protected even if it is intercepted. This additional layer of security is crucial to thwarting cyber threats.
Building redundancy into systems builds resilience, ensuring uninterrupted operations. Regular backups, stored centrally and replicated across multiple sites, mitigate the impact of cyberattacks by facilitating rapid data recovery.
Focus on passwords, authentication and security maintenance
Weak passwords present a significant vulnerability, often exploited by hackers. It is essential to eliminate default passwords and adopt strong enterprise password management solutions. Implementing two-factor or multi-factor authentication further strengthens network security.
Cybersecurity is an evolving landscape, requiring rapid application of software updates and patches from device manufacturers. Selecting providers committed to regular updates is essential to maintaining up-to-date protection.
Security audits conducted by external agencies provide insight into a company's cybersecurity posture. Using techniques such as penetration testing, these audits identify vulnerabilities, enabling targeted improvements and strengthening overall cyber resilience.
Cybersecurity measures must continually adapt to evolving threats, reflecting industries' ongoing efforts to mitigate emerging attack vectors.